Ultimately, there are ACL bits that MacOS sets and that the Macintosh Finder obeys. To solve your problem quickly, in your Terminal command line, type in 'open.' (or the path to your 'startup' folder) and that will open up the folder in your Macintosh Finder. Then do a 'Get Info' on the file: You can change your permissions here. On the classic Mac OS (the original Apple Macintosh operating system), extensions were small pieces of code that extended the system's functionality. They were run initially at start-up time, and operated by a variety of mechanisms, including trap patching and other code modifying techniques. Initially an Apple developer hack, extensions became the standard way to provide a modular operating.
On the classic Mac OS (the original AppleMacintosh operating system), extensions were small pieces of code that extended the system's functionality. They were run initially at start-up time, and operated by a variety of mechanisms, including trap patching and other code modifying techniques. Initially an Apple developer hack, extensions became the standard way to provide a modular operating system. Large amounts of important system services such as the TCP/IP network stacks (MacTCP and Open Transport) and USB and FireWire support were optional components implemented as extensions. The phrase 'system extension' later came to encompass faceless background applications as well.
Extensions generally filled the same role as DOS's terminate and stay resident programs, or Unix's daemons, although by patching the underlying OS code, they had the capability to modify existing OS behaviour, the other two did not.[dubious]
The INIT mechanism[edit]
The concept of extensions was not present in the original Macintosh system software, but the system nevertheless had a private patching mechanism that developers soon learned to take advantage of - the INIT loader. This code would search for system resources of type 'INIT', and load and run them at boot time. The code resources had to be stored directly in the Mac System suitcase's resource fork, meaning it was only really available to 'power users' who would be comfortable using ResEdit or other resource editor.
Since taking advantage of this mechanism was an unsupported hack, and only 32 INITs could be loaded in this manner, Apple responded by providing a more managed solution. Initially this itself was in the form of an 'INIT' resource with ID 31 placed in the System file that would search for further files of type 'INIT' in the System Folder, and load and run INIT resources inside them. (This is why some veteran Mac programmers still refer to the extensions loading mechanism as the 'INIT 31 trick'.[1] INITs could now be installed simply by placing a file in the System Folder, well within the abilities of the average user. Starting with System 7, extensions were relocated to the Extensions folder within the System Folder for convenience, and an auto-routing mechanism was implemented so that placing an extension into the System Folder through drag and drop would actually place the file in the appropriate subfolder.
Extensions retained the resource type of 'INIT' throughout their lifetime, and the loader was gradually enhanced to search for these resources in numerous places, including in the resource forks of control panels in a variety of formats and the Chooser.
Extensions[edit]
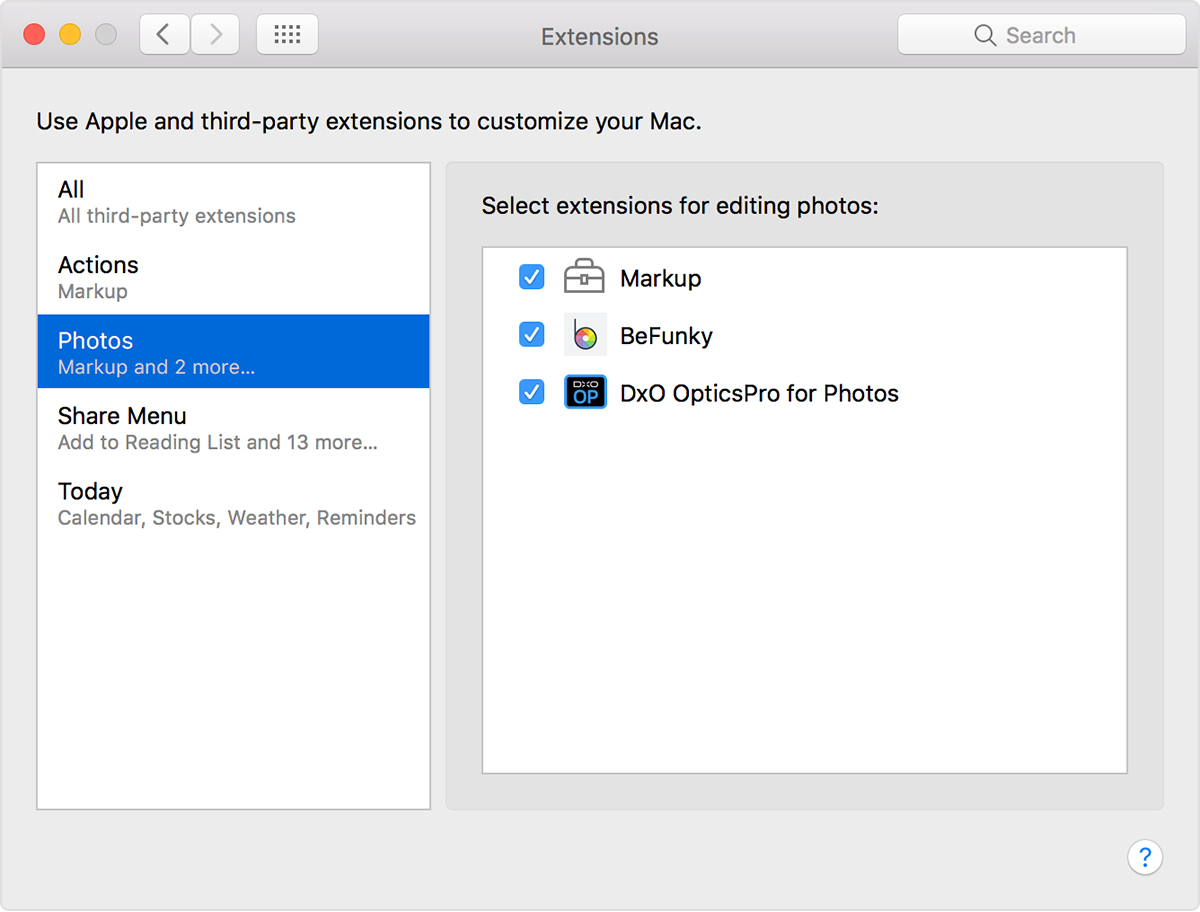
INITs evolved into system extensions, gaining additional ad hoc protocols along the way, such as supplying an icon to be displayed at boot time (the origin of this was 'ShowINIT'). The 'parade of puzzle pieces and icons' across the screen as each extension loaded became familiar to all Mac users. Apple themselves eventually released major (but optional) pieces of the operating system as extensions, such as QuickTime, QuickDraw 3D and many others. A substantial number of services and drivers in Mac OS—both official and third party—were provided as extensions, allowing for the OS to be trimmed down by disabling them.
System extensions were a common source of instability on the Macintosh, as third-party code was of variable quality and would often patch the system in ways that did not always work correctly. Some extensions didn't work properly together, or worked only when loaded in a particular order. In addition, different extensions might try to patch the same part of the system, which could lead to extension conflicts and other instability. Tracking down these sources of trouble was another task most Mac users encountered at some point. Troubleshooting Mac OS extensions could be a time-consuming process of bisecting and trial and error.
The simplest way to clean-boot the operating system was to hold the shift key: loading of extensions would be bypassed. System 7.5 added the Extensions Manager, which allowed the user to quickly enable or disable particular extensions, and also to define sets of them that would work correctly together. Extensions Manager came with two read-only base sets provided: one that contained the subset of extensions needed for basic OS operation, and one that enabled all the official extensions that shipped with the OS but disabled all third-party extensions.
The loading order of extensions was a side-effect of the GetFInfo function that was used by the loader to enumerate the files in the Extension folder. While Apple always have said that the order that results from enumeration of files using this function is undefined, on HFS volumes this function enumerated files in the order stored in the HFS catalog. People figured out that changing the first character in the file name could change the extension loading order, which caused trouble when Mac OS 8.1 moved to HFS+. Apple ended up having to change the loader to sort the filenames returned by this function into a table, and provided an interface to allow software to change the table.[2]
Configuration and control panels[edit]
System extensions had no user interface: there was no standard mechanism by which the user could configure the services provided by an extension. Extensions were able to alter the graphical interface (such as adding new menus to the menu bar) and thus accept user configuration, or they could be accompanied by an application to provide the configuration interface.
Sims 4 serial key torrent. It is a paid game, so if you want to play it, then there is a need for paying.
With System 7, control panels become separate Finder plugins on disc that could be launched by the user. By inserting INIT code into a control panel, it became possible to build extension/control panel hybrids that modified the operating system at boot time and contained their own in-built configuration interface in the same form as any other operating system control panel.
Faceless background applications[edit]
MultiFinder and System 7 and later supported faceless background applications similar to UNIX daemons or Windows Services, though using cooperative multitasking. Examples included Time Synchronizer (daylight saving time adjustment and remote time synchronization), Software Update Scheduler, and Folder Actions (folder event handling). Faceless background applications were regular applications with the restriction that they did not show up on the application menu. The only technical differences between a faceless background application and a regular application were that the 'Only background' flag was set in the 'SIZE' resource. They were prohibited from opening a normal application-level window: if they did so, the system would freeze.
They were free to open global floating windows, however, since these could neither gain nor lose focus. The Control Strip in Mac OS 8 and 9 was an example of a faceless background application that displayed a global floating window to provide user interaction. The Application Switcher was another. However, the user was not aware at any time that the Control Strip was a running process; it was simply presented as an extra interface feature. The system simply described faceless background applications as 'system applications'.[citation needed]
Language features in the Open Scripting Architecture (and thus AppleScript) were initially implemented as dynamically loadable plugins known as 'scripting additions' or OSAXes. In Mac OS 8 and 9, these were augmented by faceless background applications that were loaded in the background on demand. Just as with regular applications, these applications were accessed using tell clauses: the global namespace was not updated as was the case with OSAXes. The operating system did not indicate the launch of such processes nor indicate whether or not they were running.
Other non-INIT extensions[edit]
INIT-type extensions were loaded at boot time to update the operating system. Confusingly, various other files could be placed into the Extensions folder as well, many of which were not loaded at boot time. The most notable of these were shared libraries which were commonly put into the Extensions folder for ease of location. Shared libraries were not loaded at boot time.
INIT-type files were not the only type of system extension. Another type was scri, or WorldScript extension. The BootX Linux bootloader was implemented as a scri simply such files were loaded very early on in the boot process, before all other extensions. BootX could then display a dialog offering to let the user finish booting Mac OS or load Linux instead.
See also[edit]
- Terminate and stay resident program (DOS)
References[edit]
Home > Articles > Apple > Operating Systems
␡- Understanding File System Permissions
This chapter is from the book
This chapter is from the book
Understanding File System Permissions
The technologies collectively known as “file system permissions” are used to control file and folder authorization for Mac OS X. File system permissions work alongside the user account technologies, which control user identification and authentication, to provide the Mac’s secure multiuser environment. File system permissions—again just like user accounts—permeate every level of the operating system, so a thorough investigation of this system is required to fully understand Mac OS X.
In short, every single item on the system volume has permissions rules applied to it by the operating system. Only users and processes with root account access can ignore file system permissions rules. Thus, these rules are used to define file and folder access for every normal, administrative, guest, and sharing user. Any user can easily identify the permissions of a file or folder with the Finder’s Get Info window.
Viewing File System Permissions
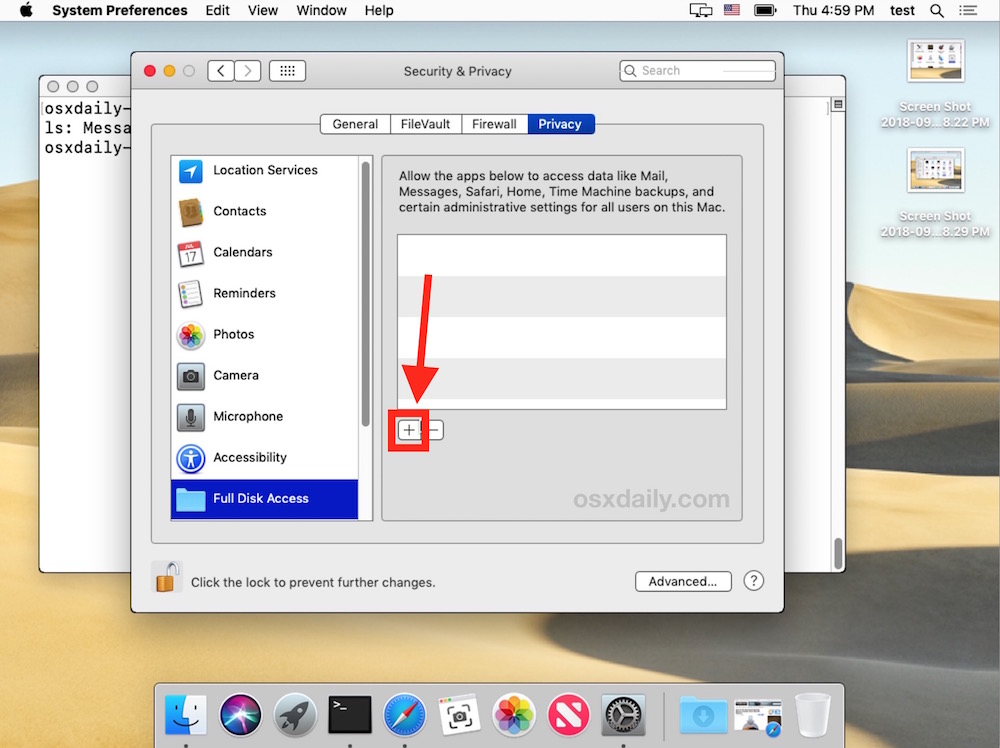
To identify file system permissions from the Finder:
- In the Finder, select the file or folder for which you wish to identify the permissions. You can select multiple items to open multiple Get Info windows.
- Open the Get Info window.
There are several methods for doing this. You can choose File > Get Info from the menu bar; use the Command-I keyboard combination; choose Get Info from the Action pop-up menu in a Finder window toolbar; or in the Finder, right-click or Control-click on an item and choose Get Info.
- Once you have opened a Get Info window, click the Sharing & Permissions disclosure triangle to reveal the item’s permissions.
Note that the permissions list is broken into two columns. To the left is a list of users or groups with access to this item, and to the right is the associated privilege assigned per user or group. Modifying these settings is covered in the “Managing Permissions” sections later in this chapter.
Ownership for Permissions
Every file and folder belongs to at least one owner and one group, and also has an ownership setting for everyone else. This three-tiered ownership structure provides the basis for file system permissions:
Owner—By default, the owner of an item is the user who created or copied the item to the Mac. For example, the user owns most of the items in his home folder. The system or root user almost always owns system software items, including system resources and applications. Traditionally, only the owner can change the item’s ownership or permissions. Despite this, Mac OS X makes management easier by giving every administrative user the ability to change ownership and permissions regardless of who the item’s owner is.
Group—By default, the group of an item is inherited from the folder it was created in. Thus, most items belong to the staff, wheel, or admin groups. Group ownership is designated to allow users other than the owner to have access to an item. For instance, even though root owns the /Applications folder, the group is set to admin so administrative users can make changes to the contents of this folder.
Everyone—The Everyone setting is used to define access for anyone who isn’t the owner and isn’t part of the item’s group. In other words, this means everyone else. This includes local, sharing, and guest users.
The simple three-tiered ownership structure presented here has been part of traditional UNIX operating systems for decades. However, with only three levels of permissions to choose from, it is quite difficult to define appropriate access settings for a computer with many user accounts and shared files, as is the case with many servers. Fortunately, as you’ll see later, access control lists (ACLs) were developed to allow for nearly limitless ownership and permissions configurations.
Traditional UNIX Permissions
Mac OS X’s basic file system permissions structure is based on decades-old UNIX-style permissions. This system also sometimes goes by POSIX-style permissions. The system may be old, but for most Mac users it is quite adequate because you can define privilege rules separately at each ownership tier. In other words, the owner, the group, and everyone else has individually specified access to each file or folder. Further, because of the inherent hierarchy built into the file system, where folders can reside inside of other folders, you easily create a complex file structure that allows for varying levels of sharing and security.
There is a variety of UNIX privilege combinations available from the command line, as discussed in the “Managing Permissions via Command Line” section later in this chapter. However, Apple has streamlined the Finder to allow only the most common permissions options.
Permissions that you can assign to a file using the Finder are:
Read and Write—The user or group members can open the file and save changes.
Read Only—The user or group members can open the file but cannot save any changes.
No Access—The user or group members have no access to the file at all.
Permissions that you can assign to a folder using the Finder are:
Read and Write—The user or group members can browse and make changes to the contents of the folder.
Read Only—The user or group members can browse the contents of the folder but cannot make changes to the contents of the folder.
Write Only (Drop Box)—The user or group members cannot browse the folder but can copy or move items into it.
No Access—The user or group members have no access to the contents of the folder.
Access Control Lists (ACLs)
Access control lists (ACLs) were developed to expand the traditional UNIX-style permissions architecture to allow more control of file and folder access. Though there is no common standard for ACLs, Mac OS X has adopted a style of ACL similar to that available on Windows-based NTFS file systems and UNIX systems that support NFSv4. This ACL implementation is extremely flexible but increases complexity by adding more than a dozen unique privilege and inheritance attribute types. Further, this implementation supports an unlimited number of ACL attributes for any user or group. Finally, it’s important to note that if an ACL rule applies to a user or group, this rule will trump traditional UNIX permissions. However, any users or groups that don’t apply to a specific ACL will still be bound by the UNIX permissions currently in place.
Apple does not expect average users to navigate through all the options available using ACLs, so once again the Finder has been streamlined to allow only the most common ACL configurations. In fact, the Finder only allows you to assign ACL attributes that match the most common UNIX permissions configurations that were previously listed in this chapter. The only feature of ACLs that the Finder actually implements is the ability to have an unlimited number of user or group privilege rules. In other words, the Finder uses the ACL architecture to let you configure unique privileges for an unlimited number of users or groups. Prior to Mac OS X v10.5, the Finder would only allow you to assign permissions using the standard three-tiered ownership style, with one owner, one group, and one setting for everyone else.
Permissions in a Hierarchical Context
It is important to remember that permissions do not exist in isolation; rather, permissions are applied in the context of folder hierarchy. In other words, your access to an item is based on an item’s permissions in combination with the permissions of the folder in which it resides. If you’re still confused, it’s easiest to think of permissions as defining access to an item’s content, not the item itself. Remember the word “content” as you consider the following three simplified examples.
Example 1: Your permissions to Example Folder 1 are read and write. It’s obvious that you should have full access to Example File 1.1, as your permissions here are read and write as well. You can also view and copy Example File 1.2, but you can’t make changes to the file’s content because your permissions are read only. Yet you can still move, delete, or rename File 1.2 because you have read and write access to the folder’s contents. Thus, File 1.2 isn’t secure in this example because you can make a copy of the original file, change the copied file’s content, delete the original file, and finally replace it with the modified copy. In fact, this is how most graphical applications save document changes; thus the file can indeed be edited.
Example 2: You have read-only permission to Example Folder 2. You can edit the content of Example File 2.1 because you have read and write access to it, but you can’t move, delete, or rename it because you have read-only access to the folder’s contents. On the other hand, you can effectively delete the file by erasing its contents. Example File 2.2 is the only truly secure file, as you’re only allowed to view or copy the file. Granted, you can make changes to the contents of a copied file, but you still can’t replace the original.
Example 3: Your permissions are identical to the first example, with one significant change. The owner of Example File 3.1 has enabled the locked attribute. Even though you have read and write access to Example Folder 3 and File 3.1, the locked attribute prevents all users who aren’t the file’s owner from modifying, moving, deleting, or renaming the file. From most applications, only the owner is allowed to change the file’s content or delete it, but the owner can also disable the locked attribute to return the file to normal. You can still make a copy of the locked file, but the copy will be locked as well. However, you will own the copy, so you can disable the locked attribute on the copy, but you still can’t delete the original locked file unless you’re the owner.
Permissions for Sharing
Once you have an understanding of the permissions options available to you in Mac OS X, you should explore how the local file system is set up by default to provide a secure environment that still allows for users to share files.
If you don’t have fast user switching enabled as outlined in Chapter 2, “User Accounts,” you should enable it now to make it easy to test file system permissions as different users. Further, to aid in your exploration of the file system you should use the Finder’s Inspector window. This single floating window, which automatically refreshes as you select different items in the Finder, allows you to quickly explore the default permissions settings without having to open multiple Finder Get Info windows. Open the Inspector from the Finder by using the Option-Command-I keyboard combination, and then click the disclosure triangle to reveal the Sharing & Permissions section.
Home Folder Sharing
Mac OS X protects the user’s files by default and allows them to be shared easily when needed. This starts with the user’s home folder. You’ll notice that users are allowed read and write access to their home folder, while the staff group and everyone is allowed only read access.
This means that every local user or guest can view the first level of every other user’s home folder. (As a reminder, guests are allowed access to your computer without a password. This is why you can disable guest access in the Accounts preferences.) The default home folder permissions may seem insecure until you look at the permissions in context. Most user data is actually stored inside a subfolder in the user’s home folder, and if you inspect those subfolders you’ll notice that other users are not allowed to access most of them.
There are a few subfolders in a user’s home folder, however, that are specifically designed for sharing. The Public and Sites folders remain readable to everyone. A user can easily share files without having to mess with permissions by simply moving the files into those two folders. Others will be able to read those files, but they still cannot make any changes to them.
Looking deeper, you’ll notice a subfolder of the Public folder is the Drop Box. This folder’s permissions allow all other users to copy files into the folder even though they cannot actually see other files in the Drop Box folder. This allows other users to discreetly transfer files without others knowing.
The Shared Folder
An additional folder set aside for sharing is the /User/Shared folder. You’ll notice that this is a general sharing location that allows all users to read and write items to the folder. Normally this permissions setting would also allow any user to delete another user’s item in this folder. Yet the Finder’s Inspector window is not showing you the full permissions picture here. There is a unique permissions setting on the Shared folder that prevents other users from being able to delete items that they don’t own. This permission setting, known as the “sticky bit,” can only be set using a command-line tool. Inspecting and changing permissions from the command line is covered in the “Managing Permissions via Command Line” section later in this chapter, and the sticky bit is specifically covered in the “Using the Sticky Bit” section later in this chapter.
Securing New Items
Once you understand how Mac OS X’s file system security architecture works with the folder hierarchy, it’s time to consider how this technology is used to secure new items. You’ve learned previously in this chapter that Mac OS X is already preconfigured for secure file and folder sharing, but you will find that new items are created with unrestricted read access.
For example, when a user creates a new file or folder at the root of her home folder, by default all other users, including guest users, are allowed to view this item’s contents. The same is true for new items created by administrators in local areas such as the root of the system volume and the local Library and Applications folders.
New items are created this way to facilitate sharing, so you do not have to change any permissions to share a new item. All that is required of you is to place the new item in a folder that other users can access; like the pre-defined sharing folders covered in the previous section. It’s assumed that if you want to secure a new item, you will place it inside a folder that no one else has access to, like your home Desktop or Documents folders.
On the other hand, this default behavior is inconvenient if you want to safely store your items in an otherwise public area, like the root of the system volume. To store items in a public area so they are only accessible to the owner requires you to change the item’s permissions using either the Finder or the command line, as outlined later in this chapter.
/nikon-nef-codec-mac-download.html. Manual Download Agreement. These Download Terms and Conditions ('Agreement') constitute a legal agreement between you (either an individual or single entity) and Nikon Corporation or its associated company ('Nikon') setting forth the terms and conditions governing your download of the operation manual for our products (“Manual”). The effects of the NEF Codec are not reflected when NEF (RAW) images are displayed in the Photo application supplied with Windows 8.1 and later. Checking the Current Version Windows 10. Right-click an NEF (RAW) image in desktop mode and select Open with program Windows Photo Viewer. Confirm that this image is displayed.
Specifically, from the Finder’s Sharing & Permissions section of the Get Info window, you must remove all other users and all group accounts from the permissions list. You cannot remove the Everyone permission, so you will have to set it to No Access. Once you have made these permissions changes, only the owner will have access to the item.
Related Resources
- Book $55.99
Permissions On Mac
- eBook (Watermarked) $55.99
Setting Permissions On Mac
- Web Edition $55.99